Posts

LINUX – nmcli command examples (cheatsheet), compare nm-settings with if-cfg file
LAN
Table of Contents
Understanding nmcli
Compare nm-settings with ifcfg-* directives (IPv4)
Compare nm-settings with ifcfg-* directives (IPv6)
Brief list of nmcli commands syntax
nmcli command examples (cheatsheet)
1. Check if…

CentOS – Installer just goes black screen on Centos8
LinuxProblem:
During installation of CentOS the installer screen goes black.
The terminal multiplexer is running in virtual console 1.
To switch from the graphical installation environment to tmux, press Ctrl+Alt+F1.
To go back to the main…

How to force fsck at every boot in Linux
Linux
In /etc/init.d/checkfs.sh is the line if [ -f /forcefsck ] || grep -s -w -i "forcefsck" /proc/cmdline, so providing forcefsck on the kernel command line or generating a /forcefsck file on shutdown should cause an fsck on the next reboot.
To…

LINUX – Network Throughput Tuning
LANGeneral Approach
To check what setting your system is using, use 'sysctl name' (e.g.: 'sysctl net.ipv4.tcp_rmem'). To change a setting use 'sysctl -w'. To make the setting permanent add the setting to the file 'sysctl.conf'.
[crayon-6a038b7b0f8e0541417736/]
More…

CentOS – How do I safely delete old kernel versions ?
Linuxpackage-cleanup:
Using package-cleanup command which is a part of yum-utils package we can uninstall any number of old kernels automatically. As an example using --oldkernels --count=2 option with package-cleanup command the command…

CentOS – NIC Teaming with LACP
LinuxA Comparison of Features in Bonding and Team
Feature
Bonding
Team
broadcast Tx policy
Yes
Yes
round-robin Tx policy
Yes
Yes
active-backup Tx policy
Yes
Yes
LACP (802.3ad) support
Yes (active only)
Yes
Hash-based…

Linux – iproute2 Cheat Sheet
LinuxOverview
iproute2 is the Linux networking toolkit that replaced net-tools (ifconfig, route, arp etc.)
Old style network utilities like ifconfig and route are still there just for backwards compatibility
and do not provide access to…
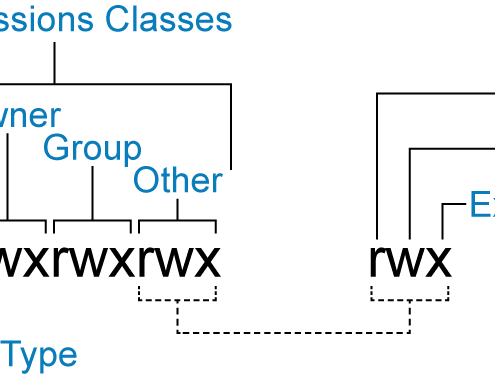
Linux – Permissions
Linux
In order to update and change file permissions, you can use the chmod command. The format of the command is as follows:
[crayon-6a038b7b13aef808658434/]
for each action
Changing Permissions
VALUE
MEANING
rwx+ugo
No…

How to Disable or Enable Disk Write Caching in Linux
LinuxATA-Based Disks
Check out whether disk caching is enabled on your disk or not:
[crayon-6a038b7b13fbe090760171/]
To disable write caching, you need to edit hdparm.conf using your favorite editor (e.g. gedit, vi).
[crayon-6a038b7b13fc8444913080/]
…
