Posts

How to force fsck at every boot in Linux
Linux
In /etc/init.d/checkfs.sh is the line if [ -f /forcefsck ] || grep -s -w -i "forcefsck" /proc/cmdline, so providing forcefsck on the kernel command line or generating a /forcefsck file on shutdown should cause an fsck on the next reboot.
To…

Linux – iproute2 Cheat Sheet
LinuxOverview
iproute2 is the Linux networking toolkit that replaced net-tools (ifconfig, route, arp etc.)
Old style network utilities like ifconfig and route are still there just for backwards compatibility
and do not provide access to…
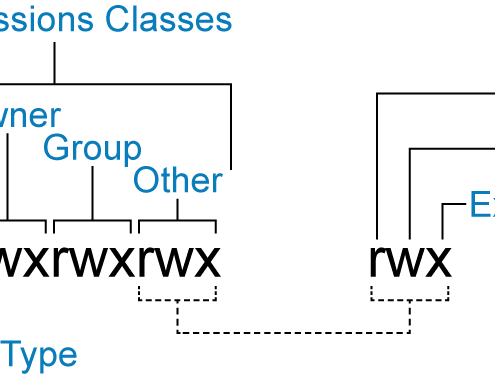
Linux – Permissions
Linux
In order to update and change file permissions, you can use the chmod command. The format of the command is as follows:
[crayon-6a24ac8c4166b623041213/]
for each action
Changing Permissions
VALUE
MEANING
rwx+ugo
No…

How to Disable or Enable Disk Write Caching in Linux
LinuxATA-Based Disks
Check out whether disk caching is enabled on your disk or not:
[crayon-6a24ac8c41ac2180487271/]
To disable write caching, you need to edit hdparm.conf using your favorite editor (e.g. gedit, vi).
[crayon-6a24ac8c41acb361799992/]
…
